After creating the new template, you will need to
configure your domain for autoenrollment. If you have already deployed
Active Directory Certificate Services for other PKI-dependent
applications, you may have already enabled this setting. If not, it can be done by performing the following:
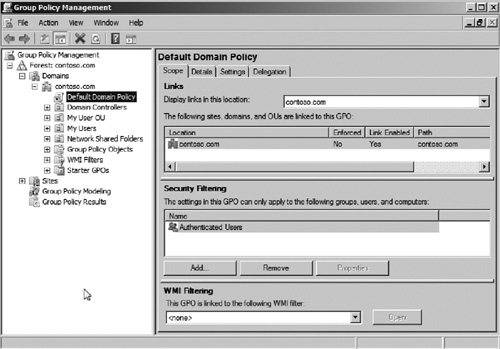
1. | Log on to a domain controller and open Group Policy Management from Start | Administrative Tools | Group Policy Management.
|
2. | Expand the nodes Forest | Domains | <your domain name> (see Figure 15).
|
3. | Right click the Default Domain policy and select Edit.
|
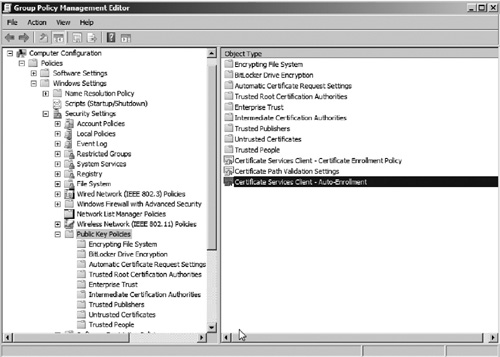
4. | Select the node Computer Configuration | Policies | Windows Settings | Security Settings | Public Key Policies.
|
5. | Open the policy object Certificate Services Client—AutoEnrollment as seen in Figure 16.
|
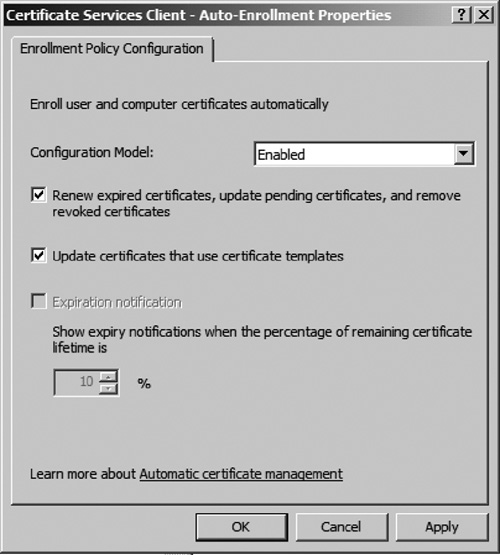
6. | Select the option Enabled. Then select both Renew expired certificates, updating pending certificates, and remove revoked certificates and Update certificates that use certificate templates options (see Figure 17). Then click OK.
|
7. | You can now force autoenrollment to occur on the hosted cache server by logging onto that server and running gpupdate from a command prompt.
|
After configuring
certificates for the hosted cache server, you need to link the
certificate to BranchCache. This is done by obtaining the SHA-1 hash
from the server’s certificate and then using the netsh command to link
the certificate. To complete this process, perform the following:
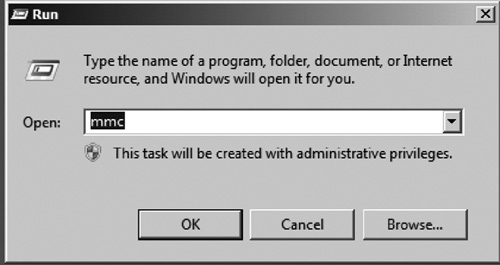
1. | Open a new mmc console by opening a new dialog from Start | Run. Then type mmc in the run prompt and click OK (see Figure 18).
|
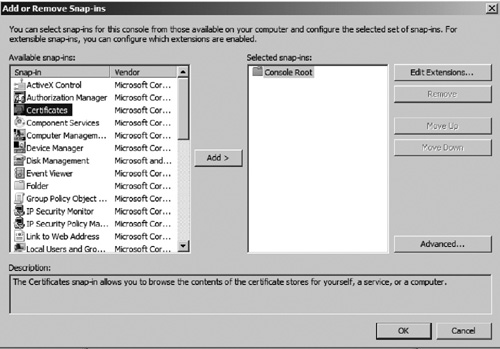
2. | From the new mmc console, go to File | Add/Remove Snap-in....
|
3. | Add the Certificates snap-in from the options as seen in Figure 19.
|
4. | When prompted whether you would like to manage certificates for user, computer, or service, select the Computer option and then choose Local Computer.
|
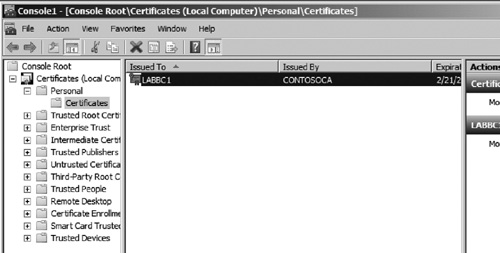
5. | From the MMC console, expand the nodes Certificates | Personal | Certificates. Then open the server certificate as seen in Figure 20.
|
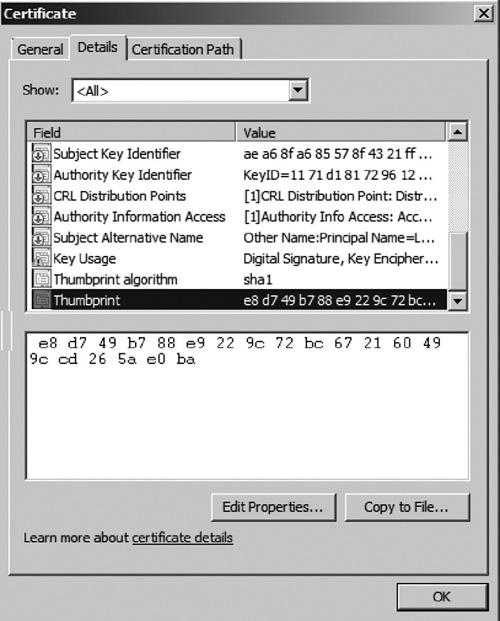
6. | Select the Details tab in the Certificate window.
|
7. | Scroll through the fields in the details view and select the Thumbprint field as seen in Figure 21.
|
8. | Copy the SHA-1 hash by selecting the hex-formatted number and using the Ctrl-C keystroke.
|
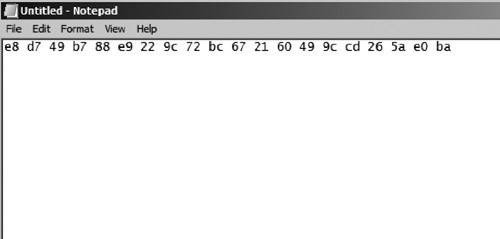
9. | Open Notepad and paste the SHA-1 hash to verify whether it has been copied correctly (see Figure 22).
Correct the formatting of the hash by removing all the spaces creating
one long hexadecimal number. This is the number we will need to link the
certificate to BranchCache.
|
10. | Open
a command prompt on the hosted cache server and enter the following
command netsh command which includes the SHA-1 hash we copied from Step 9. netsh http add sslcert
ipport=0.0.0.0:443
certhash=e8d749b788e9229c72bc672160499ccd265ae0ba
appid={d673f5ee-a714-454d-8de2-494e4c1bd8f8}.
|
You have now successfully
completed the process of setting up the BranchCache hosted cache server.
As clients begin caching files locally, they will be saved in the cache
of this server. Now, you only need to configure client computers to use
the hosted branch cache. This can be done on a Windows 7 client by
using the netsh command: netsh branchcache set service mode=HOSTEDCLIENT.
You can additionally update multiple Windows 7 clients to use the
hosted cache by deploying a GPO which can perform the same functions.